Using AWS Systems Manager to regain access to an EC2 machine
The other last night I received a call from a co-worker who added a Windows firewall rule to a production AWS EC2 machine running Server 2016. Soon after he couldn’t access the server via RDP nor were any of the IIS sites loading.
Of course a snapshot was not created prior to the change, because “It worked in Test”.
At first I thought we might be up a creek and restoring from an older backup. But, then I remembered AWS Systems Manager and the ability to send commands to an AWS EC2 machine via the AWS console.
Below are the quick steps I took to disable the Windows Firewall using AWS Systems Manager to regain access into the EC2 machine.
How to use AWS Systems Manager to send PowerShell commands to an EC2 machine
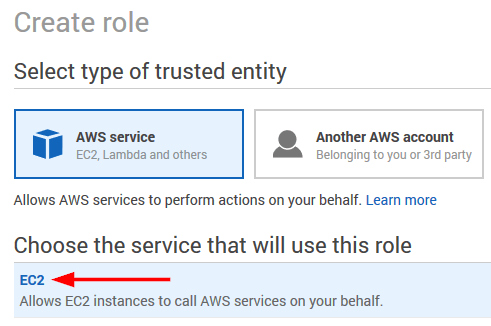
- First you need to create a new IAM Role.
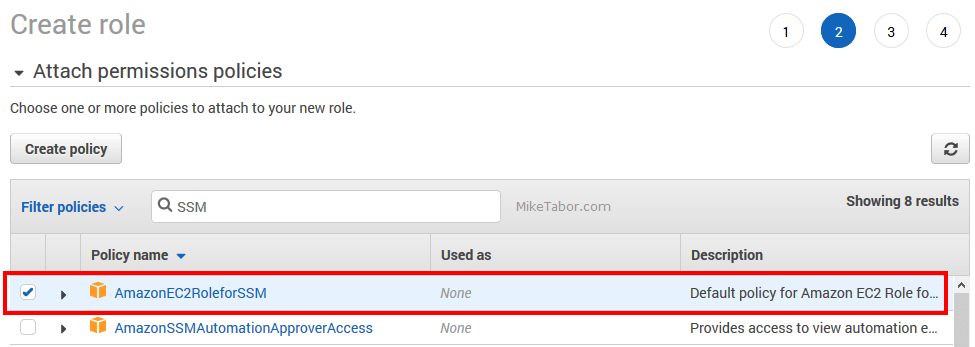
- Next attach the AmazonEC2RoleforSSM policy to the role.
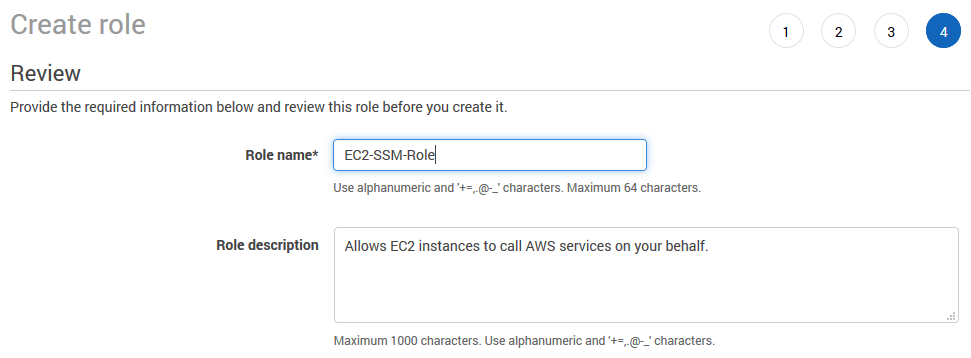
- Then name your new IAM role.
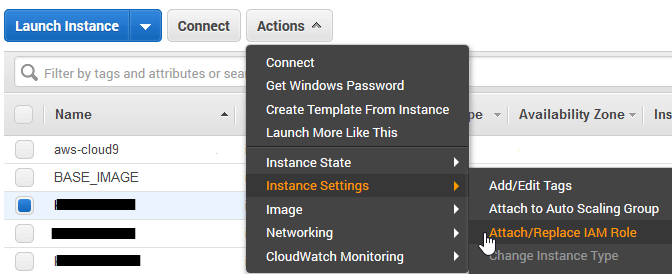
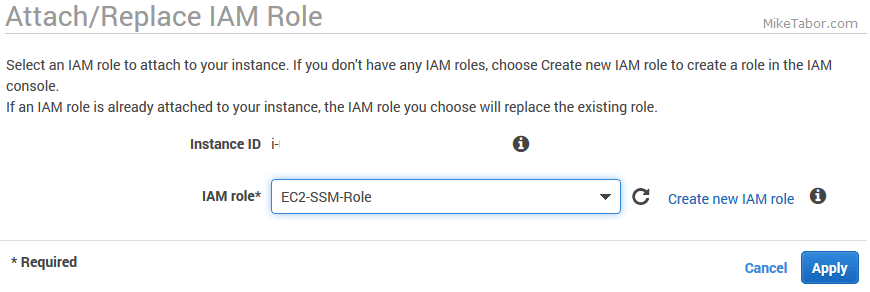
- Now in your EC2 Dashboard, select the EC2 and go to Actions > Instance Settings > Attach/Replace IAM Role.
- Select your new IAM role and click on Apply.
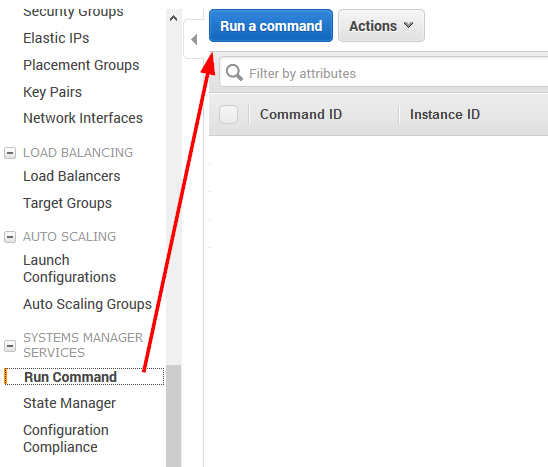
- In the left menu, scroll down to “Run Command” under Systems Manager Services and click on Run a command.
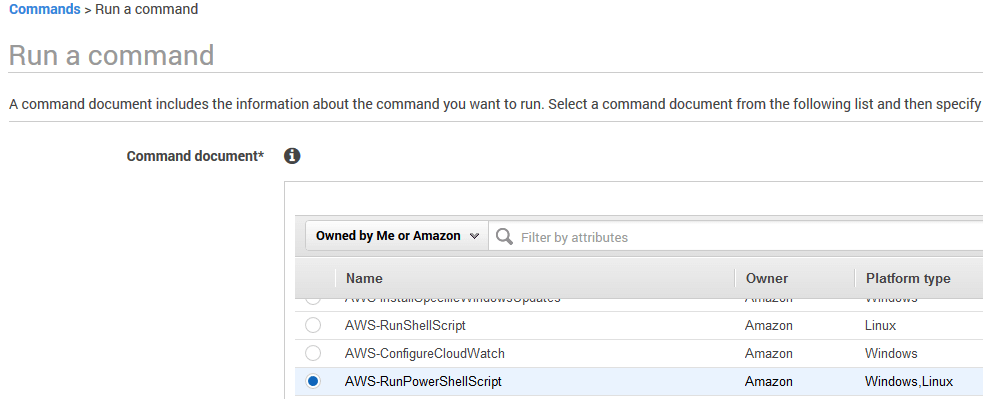
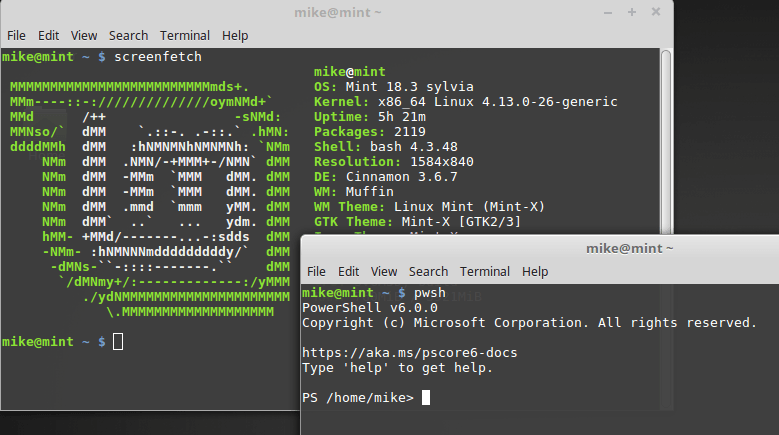
- From the Command document list select AWS-RunPowerShellScript.
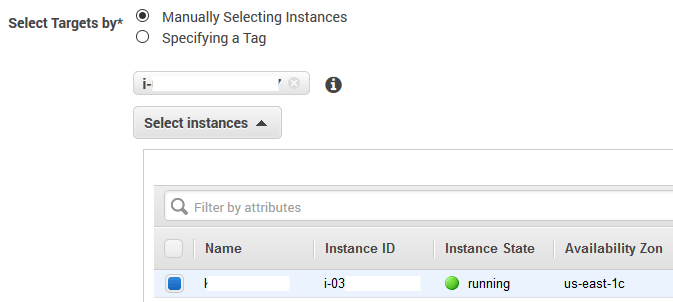
- Next select your instance you want to run the PowerShell script on.
- Finally, enter your desired PowerShell script. In this case I want to disable the Windows Firewall so I used the following code, then click on Run.
Set-NetFirewallProfile -Profile Domain,Public,Private -Enabled False
Within just a few seconds the AWS console showed the command ran successfully and we were able to get back into the EC2 machine.
As for what caused the issue in the first place, the firewall rule was mistakenly entered to block ALL ports instead of the single port that was desired and thus why RDP and the IIS pages both stopped working.



I am really happy to say it’s an interesting post to read . I learn new information from your article , you are doing a great job . Keep it up
Save my life with this :D
Haha! Well I’m glad to have helped Camilo.
-Michael